Recommendations for the Implementation of an EU Strategy on Technology Infrastructures

As technology infrastructures (TIs) are critical enablers for the European research, development and innovation ecosystems, the European Commission’s Joint Research Centre (JRC) and the European Association of Research and Technology Organisations (EARTO) recommend a pan-European, agile and sustainable environment for their development, accessibility and governance, within the framework of a dedicated EU strategy.
The key role of TIs in RD&I Ecosystems
TIs are (physical or virtual) facilities and equipment, such as demonstrators, testbeds, piloting facilities and living labs, capable of building bridges between science and the market.
They are mostly created, managed, maintained and upgraded by not-for-profit Research Performing Organisations (mainly Research and Technology Organisations – RTOs, and Technical Universities – TUs), which require dedicated and significant resources and competences.
TIs are open to a wide range of public and private users, large and small, collaborating with TI managers to jointly develop and integrate innovative technologies into new products, processes, and services.
Examples of technology infrastructures include facilities to develop electrolyser stacks, biogas plants, clean-room facilities for chip production, test areas for automated shipping or road traffic safety solutions, wind tunnels, testbeds for multi-functional nano-composites, multi-material 3D printing, thermo-plastics and industrial robotics.
Technology Infrastructures are major building blocks for Europe to deliver on its ambitions of making successful transitions to a sustainable, digital and resilient industry and society.
Industry’s innovation capacity, productivity and international competitiveness heavily depend on possibilities to develop, test, validate and upscale new technological solutions at an ever-faster pace.
Towards an EU strategy for technology infrastructures
A European Commission Staff Working Document on TIs published in 2019 recommended the development of an EU Strategy for Technology Infrastructures building on the experience and the framework of the European Strategy for Research Infrastructures (ESFRI) with its own specificities.
In this context, the JRC and EARTO launched a joint project on TIs to gather evidence and highlight the common specificities of TIs across Europe, assess the challenges they face over their whole lifecycle, and identify how their capacity could be further leveraged.
The JRC and EARTO have just published an analysis of the main strategic elements that would ensure an effective and sustainable management of an integrated landscape for TIs at the European level:
- Combining and completing the existing repositories and mappings of TIs at EU level, covering both TIs’ locations and the services and facilities they offer, could be used to enable a better understanding of the TIs’ landscape by policymakers and users, foster accessibility to TIs, and create connections between complementary TIs.
- Roadmapping of future needs for capital expenditure (CAPEX) investments in TIs should be organised with a sectorial value-chain and bottom-up approach, with the involvement of TIs’ stakeholders, by identifying the future needs for TIs in existing roadmaps linked to current EU instruments and actions (e.g. European Partnerships, European Research Area (ERA) Industrial Technology Roadmaps).
- Setting up a mechanism to draw from sectorial roadmaps and prioritise investments in TIs at European level and/or to coordinate and synchronise national/regional TIs’ roadmaps in strategic sectors would be valuable to maximise the use of public funds.
- Creating an agile Advisory Board will be necessary to operationalise the prioritisation of investments and the coordination of national/regional TIs’ roadmaps. The board should be composed of Member States experts responsible for TIs within national ministries, as well as relevant stakeholders including RTOs, technical universities, and industry (large and small).
- TIs need to be developed and upgraded at the same fast pace as the technologies and the products that are developed and tested. A strengthened and clearer pathway of grant-based public support for CAPEX investments for the creation and upgrade of TIs, as well as creating synergies for more structural support at European, national, and regional levels would be essential, as the current funding landscape is very scattered. The support for the creation of new TIs should be designed in complementarity with the support for the upgrade of existing ones, taking a balanced approach between the two.
- Pan-European accessibility to TIs should be facilitated by fostering the use of TIs in competitively funded projects at EU level, defining harmonised principles for access to TIs, and adopting a one-stop-shop approach in specific value-chains.
- Creating thematic networks of TIs with a value-chain approach would enable to better integrate and structure the European landscape for TIs, foster capacity building across regions, and spread excellence and expertise to overcome the European innovation divide. Dedicated support and funding for network orchestration activities is needed to explore the full potential of TIs’ networks.







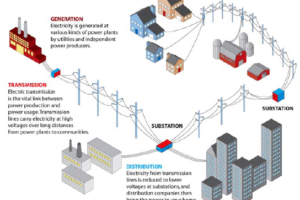
 A stable homeland is dependent on the reliable delivery of electricity—from public health to the economy and national security. According to DOE's Grid Modernization and the Smart Grid project, there are more than 9,200 electric generating units with more than 1 million megawatts of generating capacity feeding more than 600,000 miles of transmission lines that comprise the U.S. electric grid.
A stable homeland is dependent on the reliable delivery of electricity—from public health to the economy and national security. According to DOE's Grid Modernization and the Smart Grid project, there are more than 9,200 electric generating units with more than 1 million megawatts of generating capacity feeding more than 600,000 miles of transmission lines that comprise the U.S. electric grid.