CISA Announces Secure by Design Commitments from Leading Technology Providers


Cyber Security CII sector







Businesses, communities, and families across America depend on the reliable availability of oil and natural gas for countless functions of everyday life. Recognizing the criticality of the oil and natural gas (ONG) subsector to our shared security and prosperity, over 25 ONG organizations—with an emphasis on high-throughput midstream natural gas pipeline owner-operators–and their industrial control systems (ICS) vendors convened through the Joint Cyber Defense Collaborative (JCDC) to undertake the 2023 JCDC Pipelines Cyber Defense Planning Effort.
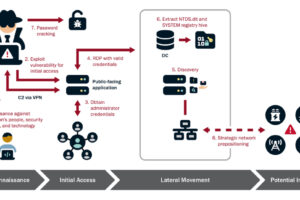
The 2023 JCDC Pipelines Cyber Defense Planning Effort was a novel approach to bring together pipeline owner-operators and their ICS vendors, in partnership with the Transportation Security Administration and Department of Energy, to address shared challenges – whether ransomware incidents like the 2021 intrusion into Colonial Pipeline or persistent targeting by threat actors like the People’s Republic of China who possess the capability to disrupt natural gas pipelines, as highlighted in the ODNI 2023 Annual Threat Assessment. An effective response to these threats demands public-private collaboration efforts to defend pipeline networks against compromise and ensure that they continue to function in a worst-case scenario.
This effort resulted in a detailed by-industry, for industry network architecture diagram and adjoining principles, the ONG Pipelines Reference Architecture. Pipeline owner-operators and ICS vendors built this architecture to serve as a voluntary model to guide their investment, planning, and operations as they work to better segment their networks and mitigate intrusion campaigns. The ONG Pipelines Reference Architecture offers practical guidance for stepping up risk management and showcases the interplay between network segmentation, multi-factor authentication (MFA), external dependencies, and critical field devices.
By organizing collaboration between midstream pipeline owner-operators and ICS vendors, this cyber defense planning effort facilitated a foundation for industry to proactively take transformative steps to harden the digital networks that run our nation’s largest natural gas pipelines against compromises – an example of the vision first established by the Cyberspace Solarium Commission and codified by Congress to catalyze cyber defense planning that yields real change in our nation’s cybersecurity.